FingBox network security appliance: Review
When you buy through links in this article, I may earn an affiliate commission. Learn More.
Securing the home network is often a black box, one which many people don’t even attempt to look into. Often their focus on network security is limited to plugging in their ISP provided router and thinking no more about it. This is pretty evident when looking at the Wifi networks in your neighborhood and seeing all the manufacturer default SSIDs. It’s a fair bet that their owners haven’t bothered to change anything else either.
For those of us more cognizant of the threats to our personal data, and the nuisance factor of someone gaining a foothold into our smart things, there is a different question: How do we know what is going on in our networks? Many routers provide some information, often in less-than-well-designed user interfaces, such as which devices have DHCP leases, but that information is often incomplete, or cryptic. Besides that, unless the network is actively monitored, it can be easy for malware or interlopers to snoop around unseen.
To address these threat, a number of consumer firewall appliance products (such as the Dojo, or Bitdefender BOX) have been entering the market which promise to keep an eye on things. The higher end router products are also starting to provide some useful features, such as better device identification, performance reporting and blocking options.
The FingBox sits somewhere in the middle. It’s certainly a network security appliance, but it’s not a firewall or router in itself. You could describe it as an independent watchdog, keeping the rest of the network in line without interfering with anything. For those wanting to make use of the growing number of connected devices to make their homes smarter, proactive security monitoring is definitely a useful addition.
I first became aware of FingBox through the standalone network scanner app, Fing, which I reviewed earlier. Fing offers some useful features, but is not very pro-active as the app can’t be monitoring the network all the time. It’s also limited by running on your smartphone, which means it can’t offer any centralized services, such as device blocking. FingBox is the crowdfunded companion, and perhaps ultimate objective, of the Fing app. As it’s now started shipping widely (their first run had some issues which needed to be addressed), I’ve now got my hands on one to review.
Because the FingBox is not a typical firewall appliance, and offers some unique features, it stands alone in the market at the moment. But just how useful is it in practice if it’s not actually handling the network traffic? We’ll take a look at each of the billed features and how they actually work, but first, the device itself.
Hardware
The FingBox is a curious little bowl shaped device that sits within a rubberized outer cover. It’s not entirely clear why this two-layered approach was taken, perhaps it’s intended to prevent cables being pulled easily as the power and Ethernet cables (included) have to be passed through the cover before being plugged into the device itself. There are no buttons or other ports, and the only user feedback is provided by a ring of colored LEDs that create a light ring around the top edge of the device. The power adapter is dual voltage and comes with interchangeable prongs. The four widely used international variants are included, which can be fitted simply by twisting the round portion of the adapter (as shown in the image) a quarter turn to click them on and off.
It needs to be hardwired into the network, but it doesn’t have any requirement to be placed anywhere in particular, unlike other security devices which need to be in the path to the internet. Once turned on, the only indication is a dim white led inside the unit. My first thought was that this doesn’t give much indication of activity, and if it wasn’t booting you wouldn’t be able to tell. After 30 seconds or so the top light rings starts pulsing green to indicate it’s in setup mode.
Here is where I had a slight issue. I had the Fing app open, and it correctly detected the FingBox and asked me if I wanted top set it up. As I was still messing with cables I indicated to do it later. However, when I went to detect the FingBox in the app a few minutes later, it wasn’t detected. A reboot solved the issue, and once set up, the light ring began flashing blue on alternating halves, indicating new devices detected on the network (naturally).
The light codes are quite extensive, and convey quite a lot of information. They’re also quite bright, but you can thankfully adjust this in the Fing app settings. The types of information covered by the light codes include such things as Speed Test in progress, DigitalFence sensing, Security Alert, and Update in progress, all in a veritable Christmas Tree of colors and pulsing, spinning glory. There is a dedicated support page for the full list.
Software
As you might imagine, all the functionality of the FingBox is surfaced through the Fing smartphone App. There are a number of tightly focused features, so we’ll look at each in turn.
Network Scanning
This is the core feature provided by the Fing app itself, but is enhanced by the FingBox by allowing the scans to be tied to the FingBox’s own view of the network. This makes it a cleaner experience, as the issue of scans being listed as different networks goes away completely. For Apple users, It also overcomes the newly introduced limitation of iOS11 by restoring access to MAC Address information to greatly improve device identification. Device identification in the app was quite good, but to me it seems even better with the FingBox. Note that the FingBox, and the Fing app, can only detect devices on the same subnet as themselves. If you’re using a guest network, or other segregated network arrangement, you won’t be able to see those devices.
All the same device information is captured as in the standalone Fing app, but as the FingBox is always watching, the logging feature is far more useful. You'll have a complete history of when each device joined the network, and came online or offline. This allows for useful notifications to be sent both via email, and through app notifications on your phone. Devices you mark as important can notify you when they go offline, and you'll be advised when any new devices appear. The latter is particularly beneficial in watching for unwanted activity and is a major benefit of such a device. You'll be immediately notified of new devices (those not previously seen by Fing) by both app notification and email.
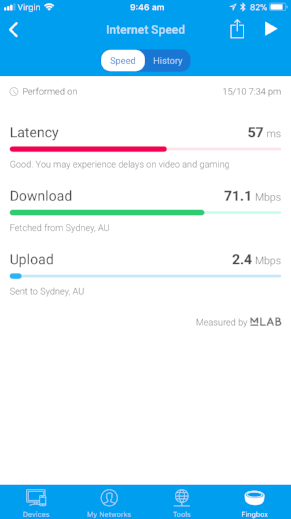
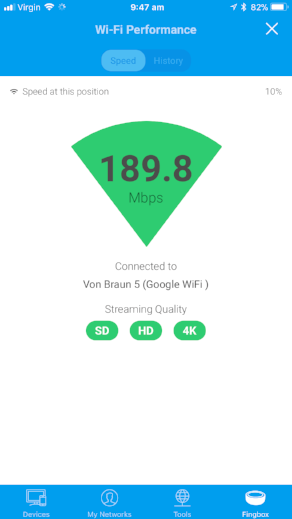
Speed Tests
Two different tests are available, one is a standard speed test, provided by mLab and provides the usual Upload, Download and Latency values. While this may be handy in some cases, it's essentially the same as the various speed tests you can run from a PC or mobile device anyway. More interesting is the WiFi performance test. This test measures the speed between a mobile device on the Wifi network and the FingBox. Since the FingBox is wired to the router, the speed measured is what the WiFi can deliver to the device running the test, and gives a practical indication of WiFi performance at that spot. This is a far more accurate indication of performance than running a conventional speed test, as it eliminates internet bottlenecks and the inherent limitation of your internet connection itself. The test runs for about a minute and updates the speed in real time, so you can walk around the house and look for performance drops, or just run the test in different rooms.
Internet Speed Test
Wifi Performance
Device Blocking
A blocked device screen
Being able to quickly and easily block a specific device from the network is a key part of the security offering in the FingBox arsenal. Unknown or rogue devices can be selectively crippled with a tap from the device list. Alternatively, just the internet access can be blocked. This is more for the parental control scenario where you might want a device to be able to continue to function on the internal network, but not have access to the internet for a time. The option to do either is fairly unique. A lot of the better routers now have the ability to block a device from the internet, but not necessarily to shut it down completely.
You can also do this at a user level. FingBox allows you to create identities for people that come into your home in a number of categories; Him, Her, Kid, Relative, Pet, and Other. These allow both filter the parental control function noted above, and allow for blocking access for a set of devices belonging to a specific person or people in one hit. Obviously, each device known to the FingBox can be assigned to one of these identities for this purpose. This is also becoming more common among the better routers by way of family blocking, schedules, and internet pause features in various forms.
In practice, this was extremely effective. The FingBox manipulates things at the data-link level (MAC Addresses), so the targeted device doesn't have any indication anything is wrong, but it's traffic is getting stalled. Testing it against my windows PC the effect was pretty much instantaneous, connections simply stopped working. Packets were still going out, but not to where they were expected to go. The main manifestation, at least from an internet user perspective, is DNS failures and connections timing out. Unblocking was equally quick, and things just started working again without any hiccups.
Digital Presence
This one is related to the identities mentioned above. Each person identity records when the person arrives or leaves the network by way of their personal devices. This allows you to see who is home, when they arrived (or left), as well as what devices assigned to them are online. While this all works, the app presentation doesn't stand out very well. Each person and device under them simply has a little time stamp (eg, 3h, 2d, etc) indicating when the device was last connected, or the person last arrived. It doesn't really show clearly when a device was actually active, and there doesn't seem to be any log of activity by person. Fing also suggests the presence feature can be used to get notifications about people's activity as opposed to individual devices, but there are no apparent settings for this.
Digital Fence
This one is a feature the Fing claims is exclusive to the FingBox. For now I'm inclined to accept that. While the device doesn't have WiFi connectivity itself, it does have what they call a 'WiFi sensor'. The purpose of this is the detect WiFi traffic in the air to identify wireless devices in range. Whether this is a full 2.4GHz WiFi radio, or some cut down receiver is unclear, but the intent is the same. The Digital Fence feature captures broadcasts from all devices in range and presents them in one of three lists: Nearby, Stations, or In my network. Alerts can be enabled for new or known devices (such as a friend or service provider) appear near your home.
At the time of writing I was unable to get this feature to work, Fing support is working the issue and I'll update when I get new information.
Update 17 Oct: After some back and forth with Fing support, I've been referred to the 'logistics team'. Evidently the belief appears to be a device fault with the WiFi sensor.
Update 4 Dec: My ticket got lost apparently, but to Fing's credit they realized and reached out to rectify. A replacement FingBox was subsequently delivered (with no requirement to send the original back) and the Digital Fence feature is now working.
The Stations feature is of particular interest. Using this you can see the name, channel and signal strength of nearby access points. This can be handy for determining possible channel conflicts with the neighbors and resolving interference issues. This can also be useful for identifying devices in your network that may be erroneously configured as ad-hoc access points. This behavior is common with many smart devices as part of their initial setup to allow communication with them to establish the connection to your actual network. Leaving such acess points open would be an issue, as they are always unsecured and any passerby could connect to them.
Bandwidth Analysis
Some routers are now able to monitor and present a decent view of device activity, both speed and volume. Obviously routers are uniquely placed to provide this information since they are the gateway to the internet, and so all traffic must pass through them. FingBox uses data-link layer analysis, similar to how it blocks devices, to monitor these values for select devices over a point in time. This provides a fairly unobtrusive way of checking on possible bandwidth hogs on the network, but requires that you have a suspicion of which ones.
How this works is by selecting the devices you want to monitor for a period of time, FingBox will then look for traffic to and from those devices and try to capture volume over time. During the analysis, the total download throughput is graphed, and the usage per selected device is shown, along with a max download speed value. The capture appears to be done over defined intervals, so the throughput values on the graph don't provide very consistent results. For example, monitoring an AppleTV streaming 1080p video from iTunes yielded very inconsistent spikes of traffic, where I would expect to see a more consistent flow. However, when the test is stopped, the total throughput for each device is presented, which does clearly indicate which (if any) was the hog for that test session.
In fairness, performing the same test with Google Wifi didn't provide much better results. The throughput was more on expectations, but still fluctuated quite a bit, and there is no actual reporting or logging functionality such as provided here. FingBox keeps the results of all tests for future reference, both upload and download volumes for each device in the selected test session.
Device selection
Bandwidth results
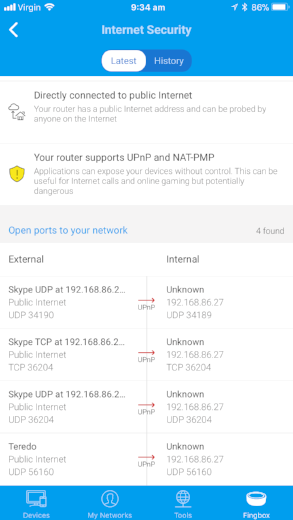
Network Security
Internet Security Report
Finally, and importantly, FingBox has some useful network security analysis capabilities. There is a proactive analysis function which gives you a report on your overall network security situation, and a reactive alerting service which monitors for a few key attack scenarios.
The Internet Security report will provide a few warnings and recommendations, such as if you have UPnP enabled. This is good to know as UPnP can be abused by malware or attackers to create additional entry points into your network. It's often recommended by security analysts to turn it off, but this tends to break things like online gaming and some streaming services which would leave most people scratching their heads. Helpfully, FingBox is also able to tell you exactly which UPnP ports are open on your network, and to where. This is something that can be difficult to determine with many routers, and it's great to have it right there, with clear identification of the ports being used.
On the reactive side, Fing claims the alerting feature monitors the network for common attacks.
“Fingbox detects the most harmful Wi-Fi attacks and offers protection against MITM (Main In The Middle) and other malicious network attacks.
”
These attacks include jamming and deauthentication, which are used to force devices to reconnect in order to capture key information for cracking. It also keeps a look out for rogue access points attempting to lure devices to connect to them instead of the legitimate access points in your network. Additionally, it monitors for invalid IP addresses being used on the network. This can be either because of rogue devices or a mis-configuration on the network itself, which can be the source of a lot of connectivity headaches.
As with new device alerts, you will be made aware of any attacks or new UPnP ports which are detected immediately by both app notification and email. This is the kind of real-time alerting which really assists in being across what is going on with your network.
Costs
The FingBox is available now on Amazon including a lifetime subscription (it’s free) to the cloud service and unlimited device tracking. The cloud service provides the device identification database, and stores network scan information as part of the Fing app.
Conclusion
For many people who haven't, or don't want to, pay out for an expensive up-market router, keeping track of their devices, usage, and security considerations can be nigh on impossible. While other security appliances are out there, they can be expensive to buy, require ongoing subscription costs, and have a negative impact on network performance or functionality. The FingBox provides a number of very useful features to keep home network users aware of what exactly is going on on their network, plus providing some value add in the form of presence tracking, and performance testing and fault finding features.
Even for those of us with expensive mesh routers that offer some of these features, such as device blocking and bandwidth monitoring, the ability to proactively be informed of devices joining the network, have a concise report of potential vulnerabilities, and have the ability to quickly respond to suspicious activity can be invaluable. For the low one-time cost, it could well be worth it.
Website: https://www.fing.io/